In recent years, there has been an increasing need to consider how we can better protect our field partners and the work that they do; particularly for those who work in more sensitive regions. So this year, we have decided to do two things.
- Be more discrete about how we refer to our field partners and the regions they work in
- Conduct cybersecurity training for field partners
For the former, we have come up with pseudonyms for our field partners rather than using their actual names and refer to the regions that they work in rather than name the actual country (e.g. Africa rather than Ethiopia, Mekong rather than Cambodia). CityLife members will find it relatively easy to work out who they are and the country they are in.
With regards to cybersecurity, the Internet and mobile technology has become an indispensable part of everyday life for people all over the world. This is true for us here in Australia and also true for our field partners who are working to share the love of Jesus through the means that God has equipped them with.
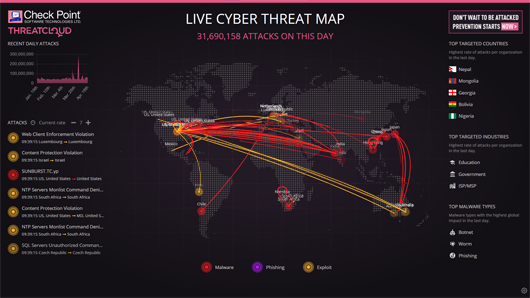
While it is true that they can research, receive information, communicate and share information over the Internet and mobile networks. It is also true that the Adversary also can use these avenues to oppose the work that our field partners are carrying out, as well as attack them personally. There are certainly malicious individuals and organisations who are out to cause harm to others for personal gain. The image in this article is from a website threatmap.checkpoint.com that shows a live map of cyber attacks are happening across the world; multiply tens of million attacks happen each day!
For this reason, we engaged the services of SecWise International to run a series of seminars to help our field partners learn about our potential vulnerabilities as we surf the internet and use our mobile phones. This seminar was run over two whole afternoons with field partners attending both in person at our CityLife Knox site, as well as over web conferencing software.
By the end of the conference, our field partners gained practical knowledge on how to secure their computers and mobile devices, as well as how to better protect their personal information over social media and popular web services.